In depth
Who governs the internet
By Jac sm Kee
Who governs the internet? How are decisions made about this key infrastructure and system that seems to support such an overwhelming part of our everyday lives? And what are feminists and women's rights activists doing about it? Jac sm Kee scans through the history of the internet to leave us thinking about who governs that space that can have such an influencing impact on so many areas of our…
In depth
Opportunities for Ecuadorian women to connect their rights online
By Flavia Fascendini
In the interview with Flavia Fascendini of GenderIT.org, Valeria Betancourt, manager of APC’s Communications and Information Policy Programme, argues that the incorporation of knowledge transfer through technology, connectivity for the information and knowledge society, and finally, inclusion and the guarantee of human rights within the broad strategies of Ecuador’s National Plan for Good Living…
In depth
Brazil, Magaly Pazello: “We have no specific debate on women's internet rights”
By Flavia Fascendini
Magaly Pazello, activist and specialist researcher in gender and information and communication technologies, recently joined the team that developed the Brazil report for the UN's Universal Periodic Review. In discussion with Flavia Fascendini, the editor of GenderIT.org, Pazello confirmed that there is still a great deal to do with regards to the connection between women's rights and a broad…
In depth
Finding the balance: Women's rights and the internet in the Philippines
By Sonia Randhawa
GenderIT.org writer Sonia Randhawa speak with Jelen Paclarin, executive director of the Women's Legal and Human Rights Bureau (WLB) in the Philippines, about the potential of the UPR to improve the lives of women in Philippines, the emerging forms of technology-related VAW and key challenges in addressing it, and the importance of women's representation in policy-making processes.
In depth
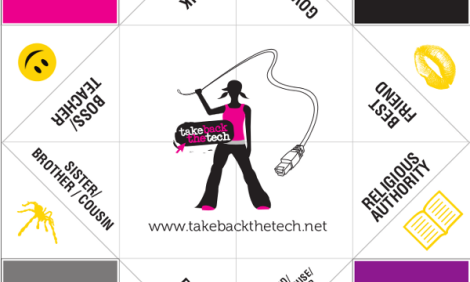
Mapping the intersection of technology and gender-based violence
By Sonia Randhawa
On 25 November 2011, Take Back The Tech! campaign launched an interactive map that allows internet users to share their stories, local news and personal experiences of gender-based violence they faced online or through the use of mobile phone technologies. As of 7 December, the map has recorded 103 stories from across the globe, with the majority of stories coming from Africa, Latin America and…
In depth
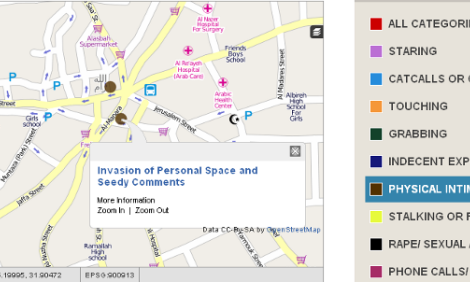
From Clock Square to StreetWatch: mapping sexual harassment in Palestina
By
Dalia Othman, a researcher and human rights activist, reports on a new initiative in Ramallah, Palestina, that uses online mapping and mobile phone technology to allow women to combat sexual harassment in the streets.
In depth
It's time to stand up and be counted
By Grady Johnson
If we want to tackle the problem of gender-based violence online, we need to develop a strong evidence base, argues Grady Johnson in this article. At the risk of revisiting old traumas, we need women to document the scope of the problem, so that the gravity of the situation can no longer be denied. Most of all, we need good numbers if we hope to make good policies.
In depth
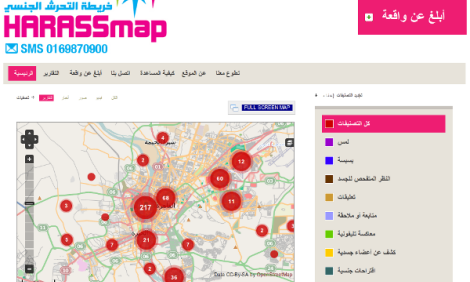
Coordinates for change: putting violence against women on the map
By Flavia Fascendini
“Map it. End it. Demand change” was the core of the Take Back the Tech! campaign for 2011. Flavia Fascendini writes about several mapping initiatives around the world that aim to document forms of violence against women so as to “put them on the map” in the sense that they are named, pointed out, shown as related, and denounced - and in that way the mapped territory is changed into one that…
Mapping and privacy: Interview with Privacy International's Gus Hosein (audio, 18 mins)
By Sonia Randhawa
GenderIT.org's writer, Sonia Randhawa, spoke with senior fellow at Privacy International Gus Hosein about how mobile devices and their ability to map our movements are intruding on women's personal privacy and individual autonomy.
In depth
Mapping and privacy: Interview with Privacy International's Gus Hosein
By Sonia Randhawa
Sonia Randhawa spoke with senior fellow at Privacy International Gus Hosein about how mobile devices and their ability to map our movements are intruding on personal privacy and individual autonomy.